

Data Confidentiality in an Electronic Environment
By Timothy J. Louwers and William M. VanDenburgh
In Brief
Data Theft Can Trigger Legal Liability
 Portable
computers have become an essential business tool for many professionals. But
a sinister threat has grown alongside the use of laptops: computer theft.
The true cost of the theft of a laptop includes not only the lost hardware
but, more important, the loss of proprietary information. The authors discuss
the best methods for laptop security, which can help CPAs decrease their risk
of potentially devastating litigation stemming from the theft of proprietary
data.
Portable
computers have become an essential business tool for many professionals. But
a sinister threat has grown alongside the use of laptops: computer theft.
The true cost of the theft of a laptop includes not only the lost hardware
but, more important, the loss of proprietary information. The authors discuss
the best methods for laptop security, which can help CPAs decrease their risk
of potentially devastating litigation stemming from the theft of proprietary
data.
Improvements in laptop computer technology have fundamentally changed the way audits are conducted. The combination of laptops’ portability, computational power, and data-handling capabilities allow auditors to set up a fully functional office anywhere. Unfortunately, the very features that make them so useful are also the source of their biggest drawbacks. Because of their portability and value, laptops are highly vulnerable to theft.
Even with an estimated 300,000 laptops stolen a year (translating into roughly $1 billion in hardware losses), the cost of a laptop is immaterial in comparison to the potential loss of proprietary data. Client information, company business plans, and other highly sensitive information are at risk. CPAs risk greater exposure than others in the business community because they are often entrusted with highly sensitive client and employer data. In addition, CPAs are required under their code of professional conduct to maintain client confidentiality. Even though laptop theft is a significant issue, laptop security is often completely overlooked. Businesses typically do not have adequate security measures in place.
Likelihood of Theft
Recent events show that laptops, by their very nature, will always remain inviting targets to low-tech criminals and high-tech industrial spies:
These cases highlight the risks that CPAs face. From consulting, auditing, and tax work, accounting professionals routinely handle many of the most confidential business transactions and data. If an accountant’s laptop is stolen (and recent figures indicate that one in 14 laptops is stolen), due diligence with respect to basic security measures must be followed and documented to avoid potential litigation resulting from the loss of confidential information.
Security Procedures
Auditors can take many steps to protect their hardware and minimize potential litigation resulting from the theft of confidential information. Measures should be taken to place restrictions on which data can be downloaded to a laptop and where laptops can be taken or stored. Data should be classified by importance, and access to highly sensitive data should be limited.
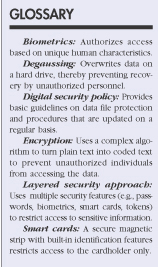
One of the first basic steps is to create a digital security policy outlining the importance of overall information security. Once established, these written information security procedures need to be continually reviewed and employees’ adherence independently verified. A copy of the company’s data policies should be distributed (and signed by employees) whenever firm laptops are issued, preferably as part of a larger training program. Vendors and contractors that need access to a company’s electronic data on a regular basis must adhere to these policies. Security procedures, such as nondisclosure statements, need to be established and enforced.
An organization can take several other steps to secure its laptops and the information contained on them. One of the easiest steps is to restrict access to working areas. Access to corporate offices needs to be regulated and controlled by keeping outside doors locked and requiring visitors to present identification and sign in. Any laptop containing sensitive data should be individually secured. For example, Intel’s CEO’s laptop is under constant human surveillance to prevent its theft. If that option is too expensive, chains or audible alarms can also provide added security.
Additional security precautions should be taken when a laptop travels. Accessing sensitive data on a flight allows unknown cotravelers to peer over one’s shoulder. Leaving a laptop visible in one’s car will almost always result in theft. Permanent identification labels, while not a deterrent, can provide for quick recovery of the stolen hardware. Encoding software on the hard drive can alert a user of a stolen laptop’s location when it goes back online. In addition, global positioning satellite (GPS) technology can make a laptop easier to find.
Password security is often overlooked. The use of simple passwords (such as one’s name or birth date) allows criminals to easily hack through this important security feature. Passwords should have at least eight characters, consisting of letters, numbers, and symbols. Restrictions can control the number of times a password can be guessed before the system is completely locked down. But passwords are only one layer of protection, and they are problematic because one tends to forget passwords that are not used often or are difficult to remember. Writing down passwords creates a security weakness; mnemonic passwords can make the procedure more convenient for users. Passwords can also be added within software programs for increased security, because even if a password is required during the machine’s startup, a thief can bypass this protection by removing the hard drive and placing it in another machine.
Other measures that limit access to data include smart cards and tokens. Smart cards have built-in microprocessors and memory used for identification purposes. Tokens generate a unique one-time password (through a challenge-response process) that authenticates the user with the appropriate token. Recent innovations include biometrics, which authenticate authorized users through their fingerprints, speech patterns, iris patterns, hand geometry, and even their scent. Some of these biometric devices are now very cost effective (often costing less than $100 per computer). Biometrics are not a panacea, however. One drawback is that the biometric systems typically compare one’s physical features with a previously made electronic version. Should the electronically stored version be compromised, the system can be overridden. For this reason, good access security dictates a layered security approach (see Exhibit 1).
The last line of defense against an industrial thief bent on stealing corporate information may be encryption. Encryption uses complex algorithms to convert data into coded text. The encryption system can be based on either a private key system (in which both encrypting and decrypting keys are kept secret) or a public key system (in which encrypting keys are made public, but decryption keys are kept secret), depending on the type of security needed. There are many good, low-cost public key encryption programs available, such as Cryptotext and PGP (Pretty Good Privacy).
Encrypted data is considered inaccessible for practical purposes. While one can break into encrypted data with enough computer resources, access to such tools is rarely available to even the most sophisticated thieves. The barrier to encryption effectiveness, however, is the need to encrypt files regularly. If an auditor leaves her laptop while working on a project without encrypting the data, then that data is unprotected. Even the most diligent users will leave some of their laptop’s data unencrypted some of the time.
Security Controls
Even if a company has written laptop security procedures, it is important to verify that such procedures are routinely followed. Security features specific to laptops used by high-ranking executives should be considered on an individual basis.
Other basic computer security steps include regular virus protection, data backup, and degaussing. Virus protection has become more important in the wake of several recent virus scares. Due to the continuous threat that new viruses pose, virus software should be updated on at least a weekly basis.
Backup procedures and policies vary greatly. Some companies have multilayered, offsite backup systems; others do not back up even critical information on a regular basis. The key questions are as follows:
Typically, it is not until it is too late that the answers to these questions receive appropriate consideration. The costs associated with electronic backup include the limitations of data storage media and the need to keep backup copies off site. These limitations are diminishing with technological advances. While data backup is critical in general computer usage (always save your files), backup becomes even more important in a portable environment. If a laptop were to be stolen, the only sure way of determining exactly what data was contained on it would be to have a simultaneous backup copy of the hard drive, perhaps on a network server.
Degaussing is the opposite of saving one’s files. When a file is deleted, only the “pointer” to the data is removed so the computer no longer knows where it is. The raw information is still there, however, and can be recovered by unauthorized individuals with the right equipment. Degaussing demagnetizes the storage medium to the point that the data can no longer be recovered. The ideal time to degauss a computer’s hard drive is after it is no longer in use, prior to its disposal or reassignment to another employee. A security checklist is provided in Exhibit 2.
©2006 The CPA Journal. Legal Notices
Visit the new cpajournal.com.